Understanding the Ransomware Attack Process
The ransomware attack process is a methodical approach utilized by cybercriminals to infiltrate, encrypt, and demand ransom from organizations. This type of cyber threat has evolved significantly over the years, growing in both complexity and frequency. Understanding this process is crucial for businesses aiming to fortify their defenses. In this comprehensive case study, we will dissect the stages of a ransomware attack, examining each step from initial infiltration to the final ransom demand. By gaining insights into these methodologies, organizations can better prepare and protect themselves from becoming victims.
Ransomware attacks typically exploit vulnerabilities within a company’s network infrastructure. Attackers employ a variety of tactics, tools, and procedures (TTPs) to achieve their malicious goals. This article will delve into each phase of the ransomware attack process, offering a step-by-step analysis of how these intrusions occur. By exploring real-world scenarios, we can provide a detailed understanding of how ransomware operates, while also discussing effective defense strategies and technologies that can mitigate these threats.
Initial Access: The Gateway to the Network
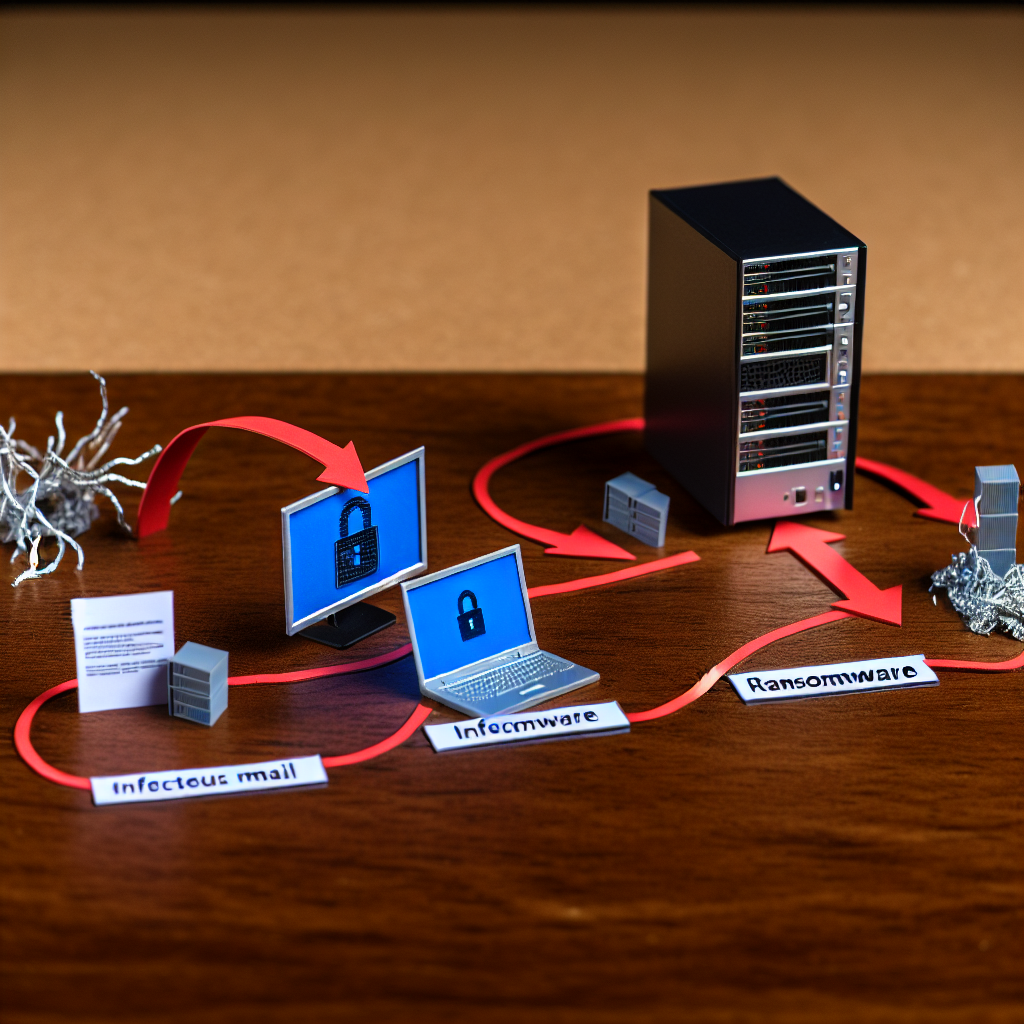
The first step in the ransomware attack process is gaining initial access to the target’s network. Cybercriminals often exploit weak points such as phishing emails, unsecured remote desktop protocols (RDP), and vulnerabilities in software applications. Phishing remains one of the most common entry methods, where attackers send emails disguised as legitimate communications to trick employees into clicking malicious links or downloading infected attachments.
Upon execution, these attachments or links deploy malware that provides the attacker with a foothold within the network. Another prevalent method is exploiting vulnerabilities in RDP, allowing attackers to brute force their way into systems with weak or default credentials. This initial access phase is critical as it sets the stage for further exploitation and lateral movement within the network.
Tools and Techniques for Initial Access
Attackers often use specific tools to facilitate initial access. These include automated scripts for email phishing campaigns and tools like Metasploit to exploit software vulnerabilities. Moreover, attackers may leverage open-source intelligence (OSINT) to gather information about the target organization, such as employee email addresses and software versions in use, which can be used to tailor their attacks.
Defensive measures must focus on strengthening email security through spam filters and employee training. Implementing multi-factor authentication (MFA) for RDP access and regularly updating software to patch vulnerabilities are also essential steps to thwart initial access attempts.
Lateral Movement: Spreading Within the Network
Once inside, the ransomware attack process moves to lateral movement. This stage involves the attacker spreading across the network to locate valuable data and gain higher levels of access. Attackers often use legitimate administrative tools like PowerShell and Windows Management Instrumentation (WMI) to move stealthily without triggering security alerts.
The aim is to identify critical assets, such as file servers and databases, that can yield substantial leverage in a ransom demand. Attackers may also escalate privileges to gain access to sensitive information and expand their control over the network infrastructure.
Detecting and Preventing Lateral Movement
Detection and prevention of lateral movement require a combination of network monitoring and endpoint protection solutions. Security Information and Event Management (SIEM) systems can play a vital role by correlating events and detecting unusual patterns of behavior. Endpoint Detection and Response (EDR) tools can monitor and respond to suspicious activities on endpoints, isolating compromised systems to prevent further spread.
Implementing a zero-trust architecture can also limit lateral movement by enforcing strict access controls and continuously verifying user identities and device integrity.
Data Exfiltration: Stealing Sensitive Information
In some ransomware attacks, data exfiltration occurs before encryption. Attackers may steal sensitive corporate data to increase pressure on the victim to pay the ransom. This phase involves transferring data from the target network to the attacker’s servers, often using encrypted channels to avoid detection.
Data exfiltration serves a dual purpose: it allows attackers to threaten the victim with data leaks if the ransom is not paid, and it provides an additional revenue stream through selling stolen data on dark web marketplaces.
Mitigating Data Exfiltration Risks
Organizations can mitigate data exfiltration risks by implementing robust data loss prevention (DLP) solutions that monitor and control the transfer of sensitive information. Network segmentation can also limit the exposure of critical data to unauthorized access.
Regular audits and data classification strategies help identify and prioritize the protection of sensitive information, ensuring that security measures are appropriately aligned with data importance.
Data Encryption: The Critical Impact
Data encryption is the hallmark of the ransomware attack process, rendering files inaccessible to the victim. Once valuable data and systems are identified, attackers deploy encryption algorithms to lock files, effectively holding them hostage until a ransom is paid.
This encryption phase is typically executed using sophisticated algorithms that are difficult to break, even with advanced decryption techniques. The attackers then generate a unique decryption key, which they promise to deliver upon receiving the ransom payment.
Protecting Against Data Encryption
To defend against data encryption, organizations should maintain regular, secure backups of critical data, ensuring that backups are isolated from the main network to prevent them from being encrypted as well. Employing real-time file integrity monitoring can also help detect unauthorized encryption activities.
Additionally, deploying endpoint security solutions with behavior-based detection capabilities can identify and block ransomware attempts before encryption occurs.
Ransom Demand: The Final Stage
The final stage of the ransomware attack process is the ransom demand, where attackers communicate their demands to the victim. This is often done through a ransom note left on the compromised systems, detailing the payment method, usually in cryptocurrency, and the deadline for payment.
Attackers may use psychological tactics to instill urgency or fear, such as threatening to increase the ransom amount or delete the decryption key if payment is not made promptly. The ransom demand marks the culmination of the attack, leaving the victim with a difficult decision: pay the ransom or attempt data recovery through other means.
Responding to Ransom Demands
Organizations should follow established incident response protocols when faced with a ransom demand. Engaging with law enforcement and cybersecurity experts can provide guidance and support during the recovery process. Paying the ransom is generally discouraged as it does not guarantee data recovery and may encourage future attacks.
Investing in a comprehensive incident response plan that includes backup recovery, communication strategies, and legal considerations is essential for minimizing the impact of a ransomware attack.
Conclusion: Strengthening Cyber Defense
Understanding the ransomware attack process is vital for developing effective cybersecurity strategies. By dissecting each phase of an attack, organizations can implement targeted defenses to prevent initial access, detect lateral movement, and protect against data exfiltration and encryption. Investing in training, technology, and incident response planning is crucial for reducing the risk and impact of ransomware attacks.
For further guidance, organizations can refer to resources such as the Cybersecurity and Infrastructure Security Agency (CISA) for detailed recommendations and best practices in combating ransomware threats. Staying informed and proactive is key to safeguarding business operations against this pervasive cyber threat.
Enhancing Security Operations with SOC Tools
Security operations centers (SOCs) play a critical role in defending against ransomware attacks. Utilizing SOC tools such as SIEM, EDR, and Security Orchestration, Automation, and Response (SOAR) can enhance an organization’s ability to detect, triage, and respond to threats effectively.
SIEM solutions aggregate and analyze log data from across the network, providing insights into potential security incidents. EDR tools focus on endpoint protection, detecting and responding to malicious activities. SOAR platforms streamline incident response by automating repetitive tasks and facilitating collaboration among security teams.
Integration and Best Practices
Integrating these SOC tools into a cohesive security strategy requires careful planning and execution. Organizations should ensure that their SIEM systems are configured to capture relevant data and generate actionable alerts. EDR solutions should be deployed across all endpoints, with regular updates to maintain efficacy against emerging threats.
SOAR platforms can be customized to automate incident response workflows, enabling faster and more efficient threat mitigation. Continuous improvement and regular validation of SOC processes are necessary to adapt to the evolving threat landscape and maintain a robust security posture.